How to protect your data with Disk Firewall
How Disk Firewall makes a difference
Being already one of the best encryption utilities on the market, Private Disk now boasts an absolutely new approach to data protection – the application level protection mechanism. The new feature called Disk Firewall is a significant addition to Private Disk 's AES strong encryption, flexibility and reliability, and it provides the highest possible level of protection, defending you from viruses, spyware, and other types of malicious software. With this new feature, businesses can not only encrypt their critical data, but ensure that it will be kept safe from both outside and inside intruders.
Disk firewall key benefits
Your key benefits of using Private Disk's innovative data protection methods are:
Hacker and virus protection
Hackers can no longer gain access to your protected data. Private Disk automatically stops viruses, Trojan horses, and worms from accessing your confidential information.
Antispyware
Your confidential information will not be sent across the Internet. Disk Firewall prevents your data being intercepted by unauthorised third parties.
Anti-theft protection
The data on employee workstations and theft-vulnerable laptop computers is encrypted using industry standard AES 256-bit encryption algorithm. With Disk Firewall, employees can access sensitive data as part of their job, but they can't run copy programs to capture the information and make illegal copies.
Cost-effective and reliable way to achieve Sarbanes-Oxley and HIPAA compliance
High-level security
Shields you from being attacked through security holes in outdated software. Disk Firewall will protect your encrypted data from viruses or other malware even if your antivirus didn't manage to detect the threat (either because of outdated virus definitions, or because of the software's inability to detect such threats)
How Disk Firewall works?
This new innovative feature is an application-level firewall that filters the requests to access the virtual encrypted disk. Below is a flowchart that shows Disk Firewall in action.
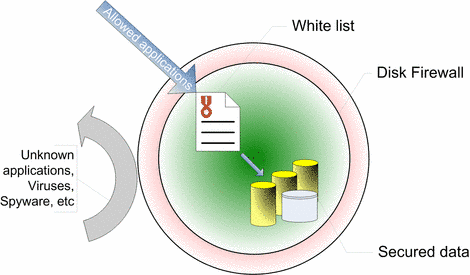
Inside the encrypted disk lies a white-list of applications (i.e. the programs that are allowed to access the contents of the encrypted drive). Whenever a program attempts to access a file on the protected drive, it is checked against the white-list. Disk Firewall uses the block if not allowed principle: if the program is not listed, its request is rejected , otherwise the program functions in a usual fashion.
This gives you several very important advantages:
- non-trusted applications do not have access to the encrypted drive in the background (this includes viruses, Trojans, spyware, etc)
- you can explicitly control which software can access the encrypted drive.
In other words, now you can be sure that you entirely control the data flow towards (and from) your protected disk.
Disk Firewall is a new technology that works under all the common versions of Windows, including the ones not supported by Microsoft anymore (ex: Windows 98).
Why would you need Disk Firewall? Examples.
If your team is working on a sensitive project using Microsoft Word and Microsoft Excel, you can ensure that team members can only use these two applications to access your files.
- They can't use Explorer to create copies of the data files.
- They can't use third-party backup programs to move copies to a floppy disc.
- They can't use your CD burner software to make copies of your data.
Below is a practical example that demonstrates the principles employed by Disk Firewall.
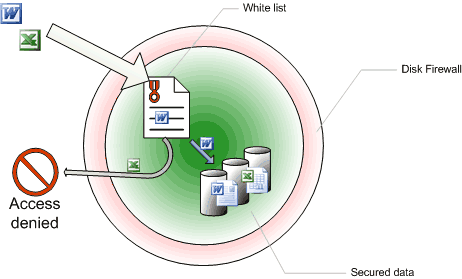
1. Assume the following conditions:
- the secured data consists of various files, including Word and Excel documents and spreadsheets;
- the white-list only contains Microsoft Word as an allowed application.
2. Two programs are trying to access the drive: Excel and Word
a. When Word tries to access the disk, Disk Firewall verifies if it is included in the white-list. The program is there, hence it is allowed to access the protected files;
b. On the other hand, Excel is not included in the list, therefore it is rejected.
The same policy applies to any other application that is not white-listed. From now on, even if you forgot to update your antivirus, or if you do not have a viable antispyware solution, Private Disk will protect your data regardless of that. This literally nullifies the risk of file corruption caused by third-party software. Download and see Private Disk encryption and firewall protection in action!
List of Services
-
Missing RegistrationRead more List Item 1
Contact us if you did not receive the registration key after your purchase
-
Berofe you contact usRead more List Item 2
How to help us help you
-
Knowledge baseRead more List Item 3
Learn how to protect your data and use our software
-
List of supported devicesRead More List Item 4
USB flash disks, smart cards, tokens, biometric devices
-
Device compatibilityRead more
Will your hardware device work with Dekart software?
-
DocumentationRead more
User guides for Dekart products
Are you sure your private data is protected?
Contact Us to Get the Solution
Sign up to our newsletter
Thank you for contacting us.
We will get back to you as soon as possible
Oops, there was an error sending your message.
Please try again later
